
In industrial and regulated environments, cybersecurity is no longer optional. Whether you operate bridges, ship locks, energy systems, manufacturing lines, or laboratory automation, you are expected to demonstrate structured risk management and resilience.
Three names appear frequently in discussions with auditors, regulators, and customers:
- NIS2
- IEC 62443
- ISO 27001
They are related, but they are not the same. Understanding the differences is crucial, especially if you work in Operational Technology environments where safety and availability are critical.
1. IEC 62443
The OT Cybersecurity Standard



IEC 62443 is a technical cybersecurity standard specifically designed for industrial automation and control systems.
It addresses:
- SCADA systems
- PLC based control systems
- Distributed control systems
- Industrial communication networks
- Embedded devices in production environments
Key Characteristics
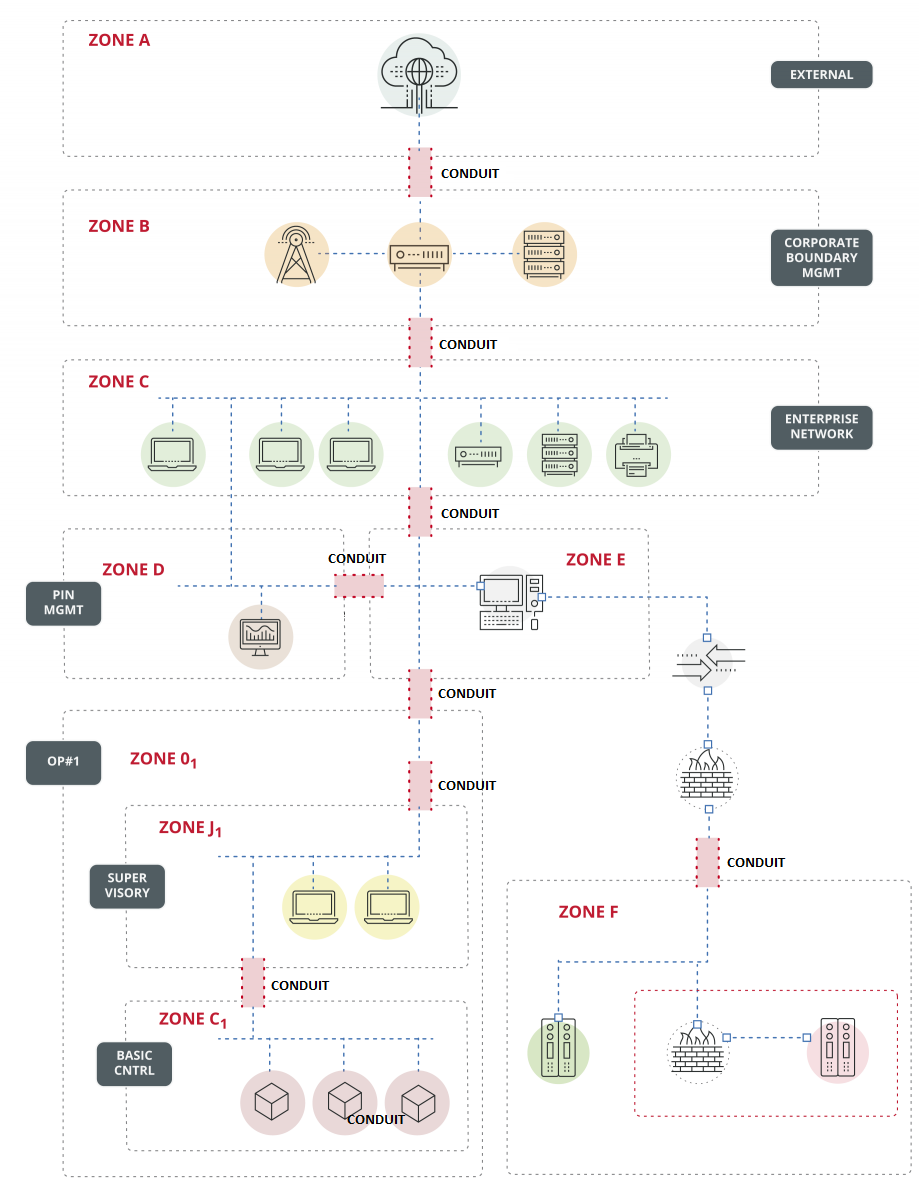
1. OT focused architecture
IEC 62443 introduces the concept of:
- Security zones
- Conduits between zones
- Security levels
This is highly relevant for real world OT systems where flat networks are unacceptable.
2. Lifecycle approach
It covers:
- Product security requirements
- System integration
- Secure development practices
- Operational maintenance
3. Technical depth
Unlike management frameworks, IEC 62443 goes deep into:
- Authentication mechanisms
- Secure communication
- Patch management in OT
- Hardening of industrial devices
In short
IEC 62443 is for engineers.
It tells you how to secure industrial systems technically.
If you work with critical infrastructure or manufacturing automation, this is your primary reference.
2. NIS2 Directive
The European Legal Obligation

NIS2 is not a standard.
It is a European directive.
It legally obliges member states to enforce cybersecurity requirements on:
- Energy providers
- Transport operators
- Healthcare institutions
- Digital service providers
- Manufacturing sectors
- Public administration
Key Characteristics
1. Legal compliance
NIS2 is mandatory once transposed into national law.
Non compliance can lead to:
- Heavy fines
- Personal liability for management
- Mandatory incident reporting
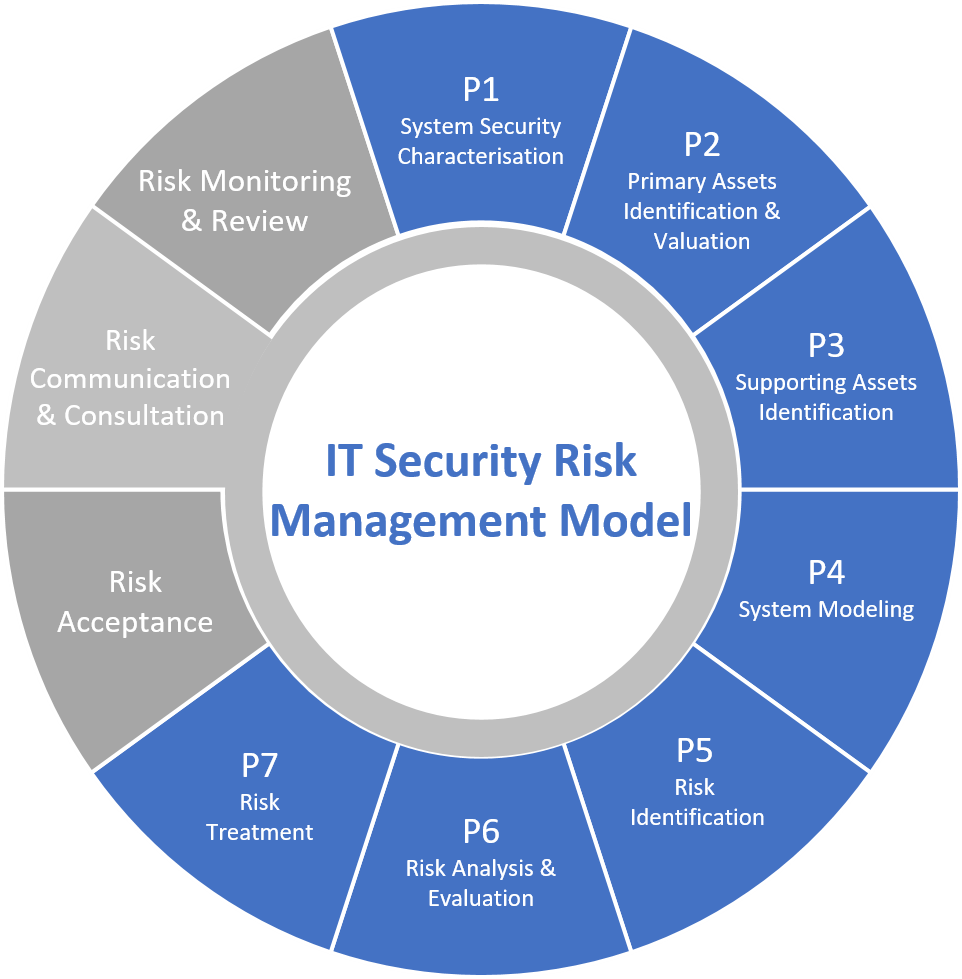
2. Risk based governance
It requires organizations to implement:
- Risk management measures
- Incident response processes
- Supply chain security controls
- Business continuity planning
3. Accountability
Management is explicitly responsible.
This changes cybersecurity from a technical issue into a board level responsibility.
In short
NIS2 tells you what must be achieved.
It does not tell you technically how to implement it.
Many organizations use ISO 27001 or IEC 62443 to demonstrate compliance.
3. ISO/IEC 27001
The Information Security Management System

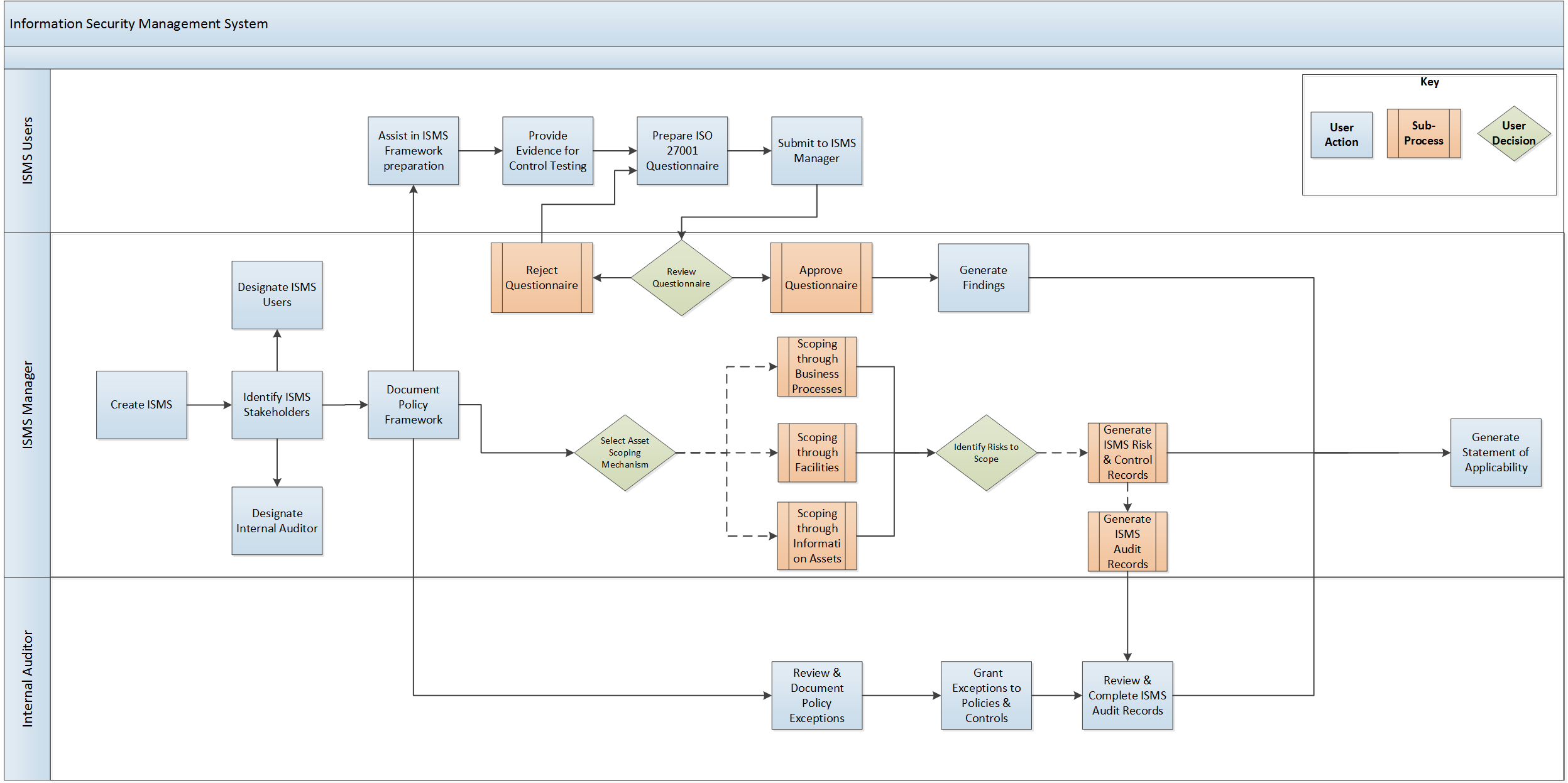
ISO 27001 is a management system standard.
It defines how to build an Information Security Management System, often called ISMS.
Key Characteristics
1. Management driven
ISO 27001 focuses on:
- Risk assessment methodology
- Policies and procedures
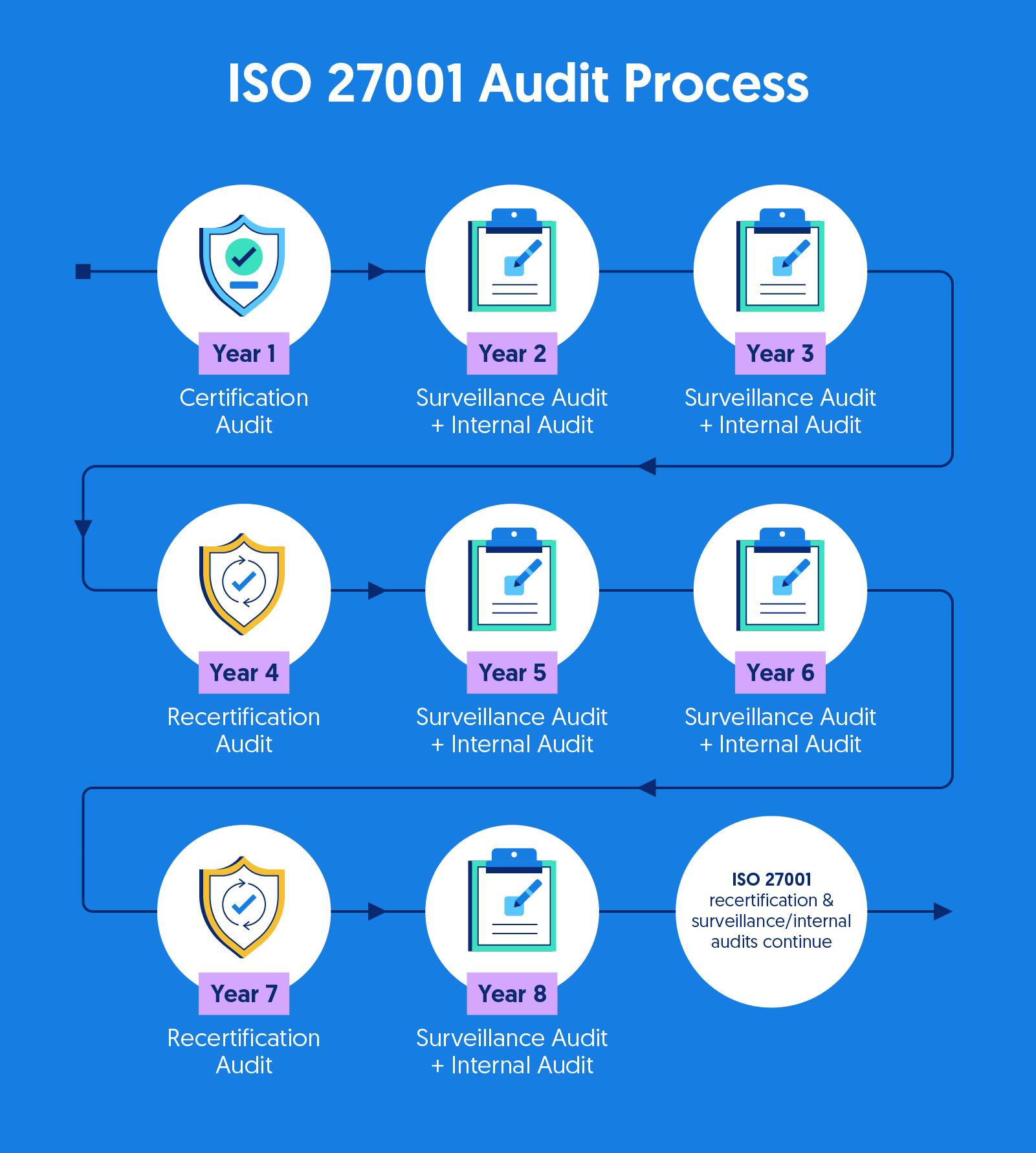
- Internal audits
- Continuous improvement
2. Certification possibility
Organizations can obtain formal certification.
This makes it attractive for:
- Consultancy companies
- IT service providers
- SaaS platforms
- Engineering companies that need to prove maturity
3. Broad scope
It applies to:
- IT systems
- Cloud environments
- Office networks
- Corporate governance
It can cover OT, but it is not OT specific.
In short
ISO 27001 is about governance and structured risk management.
It is less technical and more process oriented.
Side by Side Comparison
| Aspect | IEC 62443 | NIS2 | ISO 27001 |
|---|---|---|---|
| Type | Technical standard | EU legislation | Management system standard |
| Focus | Industrial OT security | Legal compliance | Information security governance |
| Audience | Engineers, integrators | Executive management | Management and auditors |
| Certification | Yes, product and system | No certification | Yes, organization certification |
| Technical depth | Very high | Low | Medium |
| Mandatory | Often contractual | Legally mandatory | Voluntary |
How They Work Together in Practice
In real world OT environments, they are complementary.
Example for a critical infrastructure operator:
- NIS2 creates the legal obligation.
- ISO 27001 structures governance and risk management.
- IEC 62443 secures the actual industrial systems technically.
In regulated environments, especially where availability and safety are critical, relying only on ISO 27001 is not sufficient. Technical hardening and segmentation as described in IEC 62443 are essential.
Strategic Takeaway for OT Engineers
If you operate in:
- High availability environments
- Regulated production
- Critical infrastructure
- Laboratory automation
You should understand all three layers:
- Legal layer
- Governance layer
- Technical OT layer